
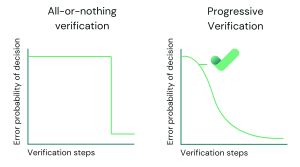
Verification is a cornerstone of security, but it can be a double-edged sword. For organisations, balancing the need for robust identity checks with the demands of usability is an ongoing challenge. Progressive verification is a flexible, layered approach that adjusts to the situation’s risk level, offering security without burdening the user unnecessarily.
This method acknowledges a simple truth: not all interactions require the same level of assurance. Signing up for a newsletter should not demand the same scrutiny as transferring funds. By tailoring verification requirements, organisations can maintain trust and safety while keeping interactions as seamless as possible.
Progressive verification builds identity assurance in steps, starting with minimal checks and escalating only when necessary. It begins with the least invasive methods, allowing users to engage with minimal friction. If the risk or sensitivity of an interaction increases, further checks are added.
This approach serves two purposes: protecting users and businesses against fraud while respecting users’ time and privacy. For example, a simple login might only require a password, but a significant transaction could prompt additional identity checks.
The first layer often involves information the user already knows, such as a username and password or answers to security questions. These checks are quick and familiar but increasingly vulnerable to breaches.
Recognising a user’s device adds another layer of security. If a login attempt comes from a recognised device, the process can remain frictionless. A new or suspicious device, however, might trigger further verification steps.
Mobile network operator (MNO) data is emerging as a valuable tool. It verifies a user’s SIM card details, detects recent changes, and validates whether the mobile number aligns with the claimed identity/KYC. This method is particularly effective for preventing APP scams, SIM-Swap fraud, authenticating returning users, and reducing friction.
OTPs sent via SMS or email are widely used for step-up verification. They offer an extra layer of assurance but should be paired with other methods to mitigate risks like phishing or number porting.
Biometric verification – fingerprints, facial recognition, or voice authentication—provides a higher level of assurance. Unlike passwords, biometrics are unique to the individual and difficult to replicate. However, they must be used thoughtfully to address concerns about privacy and data protection.
Physical security keys, such as USB or NFC-enabled devices, are among the most secure methods available. These keys act as a form of two-factor authentication (2FA) and are resistant to phishing, as they verify not just the user but also the website being accessed. They are particularly effective for protecting sensitive accounts or high-risk transactions.
For high-risk scenarios, verifying official documents, such as passports or driving licences, adds significant assurance. Users may be asked to upload images or complete a live video verification to confirm their authenticity.
Monitoring behavioural patterns, such as typing speed or mouse movements, provides a subtle layer of ongoing verification. Significant deviations from a user’s usual behaviour can flag potential fraud.
Progressive verification is not just about enhancing security – it’s about trust. By introducing measures only when necessary, organisations respect their users’ time and minimise frustration. This adaptive approach also ensures businesses can comply with regulations without alienating their customers.
Yet, challenges remain. The misuse of personal data and overly complex systems can erode trust. Striking the right balance between simplicity, security, and transparency is critical to a company’s success.
As user expectations rise, progressive verification remains a pragmatic solution for maintaining secure, seamless experiences. Verify fits into this approach as a low-friction tool along the user journey. It provides businesses with an efficient means of validating identity and assuring age by leveraging real-time insights from mobile network data. This can be particularly valuable in the early stages of progressive verification, where minimal friction is needed to confirm a user’s details.
By cross-referencing a user’s submitted details with data from mobile network operators, Verify adds an extra layer of confidence without introducing the complexity of more invasive methods. It can detect potential fraud indicators, such as SIM swaps, scam signals around APP fraud, or inconsistencies with the mobile number, ensuring businesses have accurate information to assess risk. Mobile network data can also be used to verify the device in session, without the need for an OTP, giving you a more complete picture of identity.
Last updated on January 6, 2026



Verify offers a vast range of data intelligence around a customer’s mobile number. It helps you confirm a customer’s identity to assess the authenticity of a mobile number and identify any suspicious activity
Check out VerifyWe provide the most comprehensive device, network and mobile numbering data available
Contact us > Chat to an expert >